As you advance your IT career, there are certain certifications that will give you higher earning potential. The cybersecurity field is in need of qualified IT security professionals – there are more jobs than candidates for them right now. And the demand continues to grow as cyber criminals get smarter and bolder. With so many IT cybersecurity certifications available, it’s hard to know which ones are going to help you earn a better living than others. Help combat cyber criminals and earn a healthy salary at the same time with the certifications that top our list.
TrainACE - IT and Cybersecurity Training Blog
Top 5 Highest Paying Cybersecurity Certifications
[fa icon="calendar'] Jan 6, 2017 9:49:21 AM / by The TrainACE Team posted in CEH, CISM, CISSP, Cybersecurity, CISA
CEH vs. OSCP: A Modern Analysis for the Career-minded Professional
[fa icon="calendar'] Dec 21, 2016 9:01:08 AM / by Jeff Rinehard posted in CEH, EC-Council, Ethical Hacking
Rising to the surface in a sea of cybersecurity hiring candidates demands more than mere skill. Employers demand stronger assurances, and the best guarantees of employee talent come in the form of certifications.
Choosing between obtaining Certified Ethical Hacker and Offensive Security Certified Professional credentials may seem difficult to the uninitiated. Here's some vital clarification on which certs will help you outswim your professional peers.
Information Security Certification Path After Security+
[fa icon="calendar'] Sep 29, 2015 11:41:39 AM / by Ariana Ciancio posted in CASP+, CEH, Cisco, CISSP, CompTIA, Cybersecurity, EC-Council, Security+
As an entry-level certification for information security jobs, Security+ will get your foot in the door for a promising career. But why stop there? If you are looking to advance your information security career, you should treat the Security+ certification as just a first step on the job path. In order to be more marketable as an experienced security professional as well as more valuable to current employers, consider advancing your proficiency in information security with additional training and certifications! The following options will validate your further expertise of information security and can increase the chances of promotion opportunities and salary increases! If information security is an industry worth pursuing to you, then keep reading to learn how to make the most out of your career!
Ethical Hacker Job Opportunities
[fa icon="calendar'] Aug 19, 2015 11:30:20 AM / by Alexandra Ducane posted in CEH, EC-Council, Ethical Hacking
Updated for 2022. As innovation in the technology field accelerates and becomes increasingly sophisticated, there are many new, exciting devices and gadgets hitting the market. While these advancements in technology have offered society a tremendous level of convenience, on the flip-side they open more opportunities for hackers. These bad actors are constantly looking for ways to exploit new systems to their benefit at the expense of innocent victims, such as card skimming and other forms of cyber crime.
With the exponential growth in advanced technology, comes increased risk of cybersecurity breaches. The demand for qualified personnel who can assess these vulnerabilities and help fix them is at an all-time high in the Washington, DC, region. So, if you're thinking about a career in ethical hacking, there is a lot to gain by obtaining the CEH certification, and understanding some of the roles you could apply for once you have it.
Here we'll break down some of the more popular job opportunities available to those with the Certified Ethical Hacking (CEH) certification!
Why a Career as an Ethical Hacker is Awesome
[fa icon="calendar'] Nov 10, 2014 9:00:28 AM / by Jackie Somma posted in CEH, EC-Council, Ethical Hacking
Don't do the crime if you can't do the time.
Ethical Hacking Tools and Techniques
[fa icon="calendar'] Apr 4, 2014 8:00:16 AM / by Alexandra Ducane posted in CEH, EC-Council, Ethical Hacking
Top 7 Tips for Ethical Hacking
[fa icon="calendar'] Feb 11, 2014 9:43:16 AM / by Max Fonrose posted in CEH, EC-Council, Ethical Hacking
Do you possess any of these traits? Enterprising. Investigative. Inquisitive. Curious. Methodical. Calculated. Patience. Does this sound like you? Do you get excited thinking about firewalls and encrypted websites? Are you interested in being one of the good guys that help stop criminal hackers? If you fit this description, you probably are an ethical hacker or you have what it takes to become one. Do you think you have the potential to be an effective ethical hacker?
CEH Prerequisites for Training and Certification in 2021
[fa icon="calendar'] Dec 4, 2013 11:30:06 AM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
(** Updated March, 2023)
EC-Council's CEH Certification has become the must-have accreditation if you want to become a certified ethical hacker. While you can jump right in and take the exam with limited experience, there are some necessary CEH prerequisites and some recommended ones. Here's a breakdown of what ethical hacking is and our recommended CEH prerequisites.
The Steps to Becoming a Penetration Tester
[fa icon="calendar'] Nov 22, 2013 9:35:26 AM / by The TrainACE Team posted in CEH, Cisco, Online Training, Pentesting, Programming
https://www.trainace.com/products/ceh-certified-ethical-hacker-training-and-certificationAccording to statistics provided by GO-Gulf.com, the cost of cyber crime will top $100 billion this year. Cyber crime affects 18 victims per second for a total of around 556 million victims per year. Just recently, the FBI warned that cyber attacks have eclipsed domestic terrorism as the primary threat to U.S. security. Penetration testers use their skills to help organizations fix vulnerabilities in their systems. But what are the steps to becoming a penetration tester?
CEH Practice Test
[fa icon="calendar'] Nov 20, 2013 11:30:13 AM / by alan posted in CEH, EC-Council, Ethical Hacking
The vision of a hacker sitting in a darkened room pecking away on a keyboard with computer code scrolling down three separate monitors morphs to an invaluable member of the business world. Legal hacking grabs the attention of many who want to use their computer coding and puzzling skills to earn a living instead of running from the law.
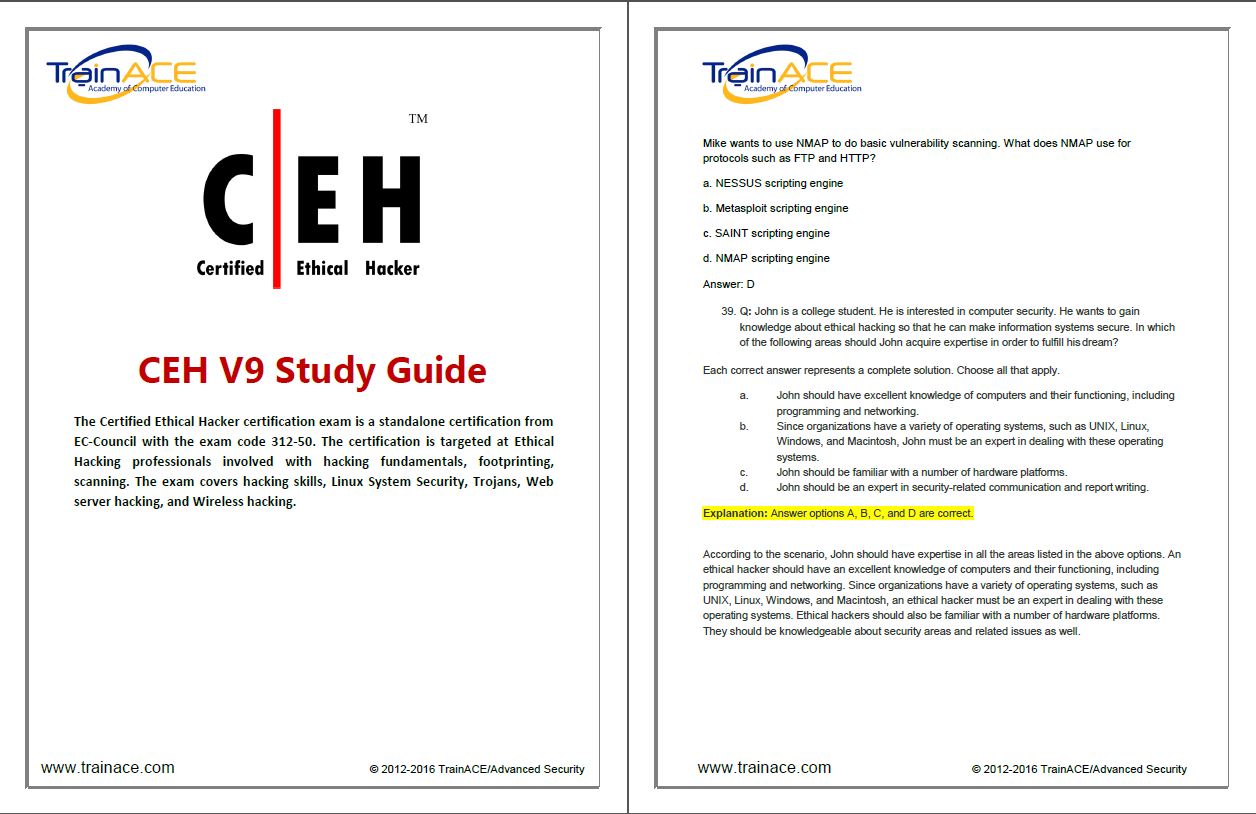
CEH Training Materials
[fa icon="calendar'] Nov 6, 2013 11:01:33 AM / by alan posted in CEH, EC-Council, Ethical Hacking
Being a certified ethical hacker is an in-demand career. While relatively new, the need for it can't be underestimated. These are the people who can beat unethical hackers, because they know the things those hackers know and can think like them. There are now classes around the world that will teach you to become a certified ethical hacker. Once you're certified, you can get a job with almost any company that uses technology that is prone to hacking. To become certified, however, you have to pass a certification exam at the end of your training course.
CEH Training Study Guide
[fa icon="calendar'] Oct 30, 2013 11:30:34 AM / by alan posted in CEH, EC-Council, Ethical Hacking
Certified Ethical Hackers (CEH) can be very beneficial for companies. By applying their training as hackers for the good of organizations, they can help test firewall systems as well as other network security features to find vulnerabilities. This knowledge can then be used to help people withstand real attacks from others with nefarious motives.