The Security+ certificate provided by CompTia is something that major companies require for a wide variety of different vendors who work in the cyber security and tech sectors of their company. It doesn’t matter how much experience a worker has in these fields—if they don’t have this certificate they won’t be hired for a job in most cases. Therefore, if someone wants to work for the department of defense for any government or a United States defense contractor, they need to pass the test and obtain the CompTia Security+ certificate.
TrainACE - IT and Cybersecurity Training Blog
alan
Recent Posts
Security+ Exam Cost
[fa icon="calendar'] Mar 5, 2014 11:30:57 AM / by alan posted in CompTIA, Cybersecurity, Security+
Security+ Practice Test
[fa icon="calendar'] Feb 19, 2014 11:30:42 AM / by alan posted in CompTIA, Cybersecurity, Security+
Certificate of Validity
The Security+ Practice Test is a well-known valuable asset within the IT Industry. A reason for obtaining such certification is to enhance your professional profile within the information technology industry. IT Security is growing at an increasing rate, meaning more jobs for those with proper credentials and qualifications. As a $60 billion industry with rapid growth, certification of authenticity will give your resume that extra boost in a demanding field.
Security+ Training Materials
[fa icon="calendar'] Feb 5, 2014 11:30:11 AM / by alan posted in CompTIA, Cybersecurity, Security+
There is an ever increasing demand for security specialists to handle computer privacy in all industries. This is because of the complexities involved in the IT world and the many challenges that present themselves each day. A good specialist is as good as the study materials used for training. However, computer privacy isn’t all about passing the examination. It’s true to say that knowledge is what is left after all examinations as this is what makes a good Security + specialist.
CEH Practice Test
[fa icon="calendar'] Nov 20, 2013 11:30:13 AM / by alan posted in CEH, EC-Council, Ethical Hacking
The vision of a hacker sitting in a darkened room pecking away on a keyboard with computer code scrolling down three separate monitors morphs to an invaluable member of the business world. Legal hacking grabs the attention of many who want to use their computer coding and puzzling skills to earn a living instead of running from the law.
CEH Training Materials
[fa icon="calendar'] Nov 6, 2013 11:01:33 AM / by alan posted in CEH, EC-Council, Ethical Hacking
Being a certified ethical hacker is an in-demand career. While relatively new, the need for it can't be underestimated. These are the people who can beat unethical hackers, because they know the things those hackers know and can think like them. There are now classes around the world that will teach you to become a certified ethical hacker. Once you're certified, you can get a job with almost any company that uses technology that is prone to hacking. To become certified, however, you have to pass a certification exam at the end of your training course.
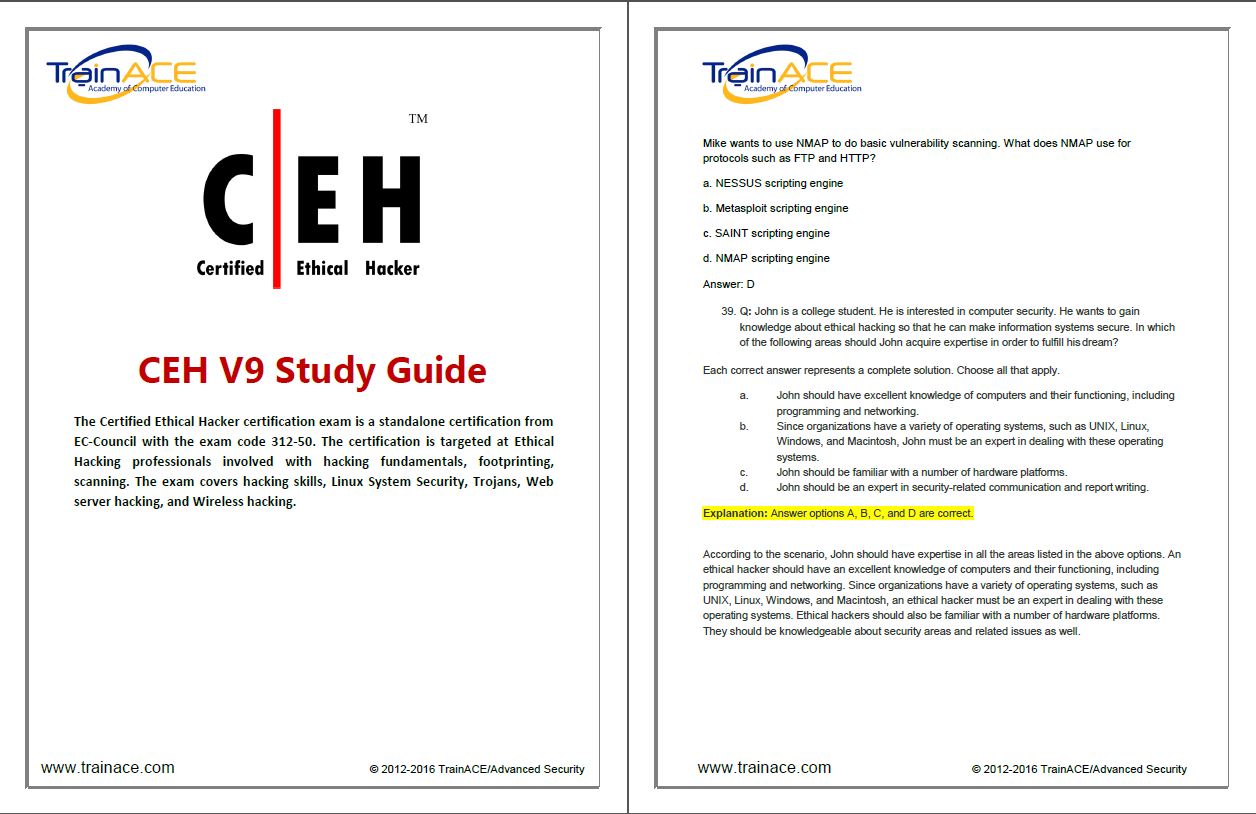
CEH Training Study Guide
[fa icon="calendar'] Oct 30, 2013 11:30:34 AM / by alan posted in CEH, EC-Council, Ethical Hacking
Certified Ethical Hackers (CEH) can be very beneficial for companies. By applying their training as hackers for the good of organizations, they can help test firewall systems as well as other network security features to find vulnerabilities. This knowledge can then be used to help people withstand real attacks from others with nefarious motives.
CEH Training Books
[fa icon="calendar'] Oct 23, 2013 11:30:19 AM / by alan posted in CEH, EC-Council, Ethical Hacking
In order to be prepared for Certified Ethical Hacking exams, you should invest in quality reading material. Training books on the market can provide you with everything you need to know in order to prepare for a career in CEH. After you have completed your exams, keeping your CEH books on hand for future reference is recommended. However, you'll need to keep up to date with current editions for well used books, as information in the CEH industry changes regularly. Here are some of the top texts you can use for CEH training and exam preparation.