TrainACE - IT and Cybersecurity Training Blog
Breaking Into Ethical Hacking by Overcoming the Biggest Hesitations
[fa icon="calendar'] Sep 11, 2025 4:30:22 PM / by Paul Ricketts posted in EC-Council, Ethical Hacking
Your Guide to CEH and CHFI Certifications: Mastering Cybersecurity with EC-Council
[fa icon="calendar'] Mar 19, 2024 4:23:04 PM / by Paul Ricketts posted in CEH, CHFI, EC-Council, Ethical Hacking
In the rapidly evolving field of cybersecurity, the demand for skilled professionals who can defend digital assets against cyber threats is at an all-time high. In our years of experience, two certifications that stand out for individuals looking to make their mark in this domain are the Certified Ethical Hacker (CEH) and the Computer Hacking Forensic Investigator (CHFI) certifications offered by the EC-Council. These certifications validate your cybersecurity and forensic investigation expertise and open doors to numerous high-profile jobs in the IT security sector. Let's dive into our guide that outlines a training strategy for these in-demand EC-Council certifications, emphasizing learning hacking skills, mastering tools and techniques, and leveraging hands-on labs and practice environments.
How to Become a Certified Ethical Hacker
[fa icon="calendar'] Apr 21, 2021 11:37:56 AM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
In recent years becoming a certified ethical hacker has become a much sought-after skill in the cybersecurity world. Seeded by small groups of early hackers who bucked the trend of hacking for financial gain or simple disruption, it took time for the practice to be accepted as a legitimate role in the business world.
But how do you become a certified ethical hacker?
Is CEH Certification Worth It in Maryland?
[fa icon="calendar'] Jun 1, 2020 1:17:39 PM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
EC-Council's Certified Ethical Hacker (CEH) certification first launched in 2003. Since then, it has been continuously updated and is now in its 10th edition. The certification is designed to test your ability to use the knowledge and skills of malicious hackers to help organizations lawfully identify vulnerabilities within their systems before cyber-criminals can exploit them. CEH is considered a great starting point for IT technicians looking to develop computer forensic and penetration testing careers. Training for CEH takes time and effort, so is CEH certification worth it?
The Cost Of CEH Certification and Training in 2021
[fa icon="calendar'] Mar 25, 2019 1:38:00 PM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
Updated June, 2021 - Information security professionals are in high demand — job opportunities and salaries are on the rise as organizations seek top talent to help defend cloud-based networks, improve application security, and develop innovative threat-reduction strategies.
The caveat is that field experience isn’t enough; companies want candidates whose qualifications include on-the-job training and industry-leading certifications. One of the most in-demand is the CEH certification.
Here’s a breakdown of the cost of CEH certification and how to get started.
What You Need to Know about CEH Certification
[fa icon="calendar'] Mar 12, 2019 1:22:03 PM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
So, you’re excited about the possibility of getting into an ethical hacking career. You love the idea of using hacker’s tactics legally to help others protect themselves from cyber attacks. You’ve heard about CEH certification, but you’re not sure what it is or why it’s important to you as a potential ethical hacker.
Let’s break down EC-Councils’ CEH certification and why it’s an essential tool in a cybersecurity career.
Understanding Ethical Hacking
[fa icon="calendar'] Dec 6, 2018 4:30:37 PM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
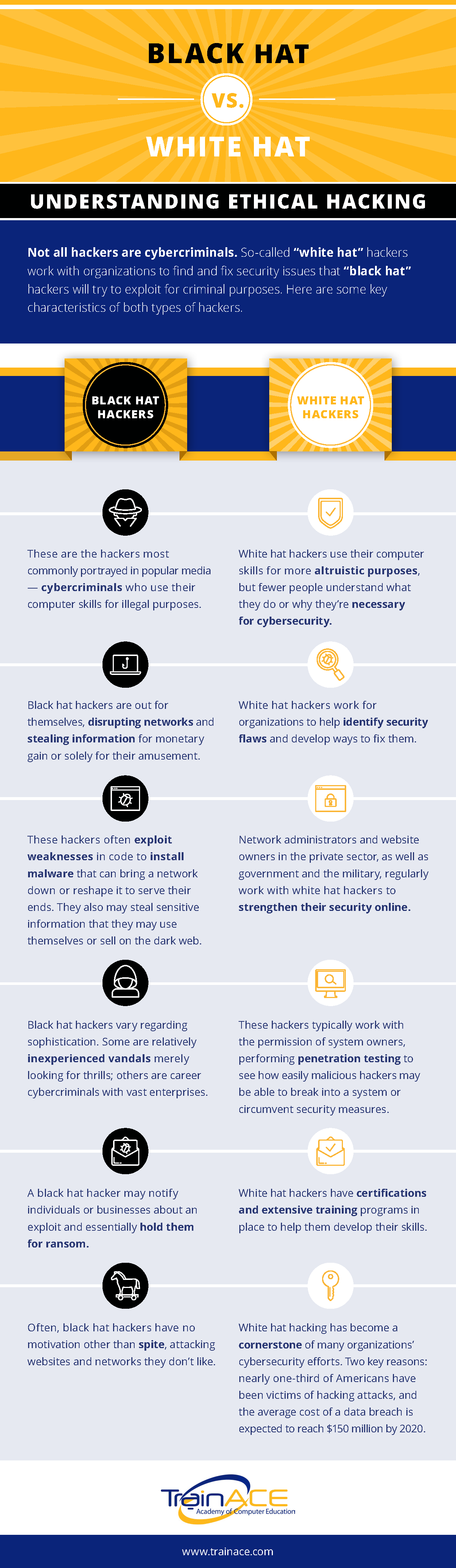
Not all hackers are cybercriminals. Increasingly, businesses around Washington DC, Maryland, and Virginia employ ethical hackers (also known as white hat hackers) to break into their computer networks to expose vulnerabilities. Ethical hacking and penetration testing have become a mainstream career within the region, with companies employing a highly skilled cohort of programmers and computer experts.
Let’s explore the basics and increase your understanding of ethical hacking. We’ll lay out the differences between Black Hat and White Hat hackers, differentiating between cybercriminals and ethical hackers.
7 Reasons Why Hackers Should Get An Ethical Hacking Certification
[fa icon="calendar'] Mar 16, 2018 1:53:42 PM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
According to the 2018 Hacker Report less than 5% of today’s ethical hackers learned their skills in a classroom. While the majority of ethical hackers do have some form of computer qualification, few have formal certification in the discipline itself. So why would an ethical hacker need anything as ‘establishment’ as formal ethical hacking certification?
The Average Salary of a Certified Ethical Hacker (CEH) in 2023
[fa icon="calendar'] Sep 25, 2017 11:12:27 AM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
(**Updated in April, 2023)
It's becoming increasingly evident that the internet is playing an ever-growing role in our lives, from grocery purchases to healthcare advice. The COVID-19 pandemic has only accelerated this transition. At the same time, the volume and sophistication of cyber-attacks have also increased, with cybercriminals taking advantage of increased vulnerabilities due to most of us working from home on less-than-ideally-secured networks. So, as an IT professional, what can you do to positively impact an increasingly insecure world while improving your financial standing?
CEH vs. OSCP: A Modern Analysis for the Career-minded Professional
[fa icon="calendar'] Dec 21, 2016 9:01:08 AM / by Jeff Rinehard posted in CEH, EC-Council, Ethical Hacking
Rising to the surface in a sea of cybersecurity hiring candidates demands more than mere skill. Employers demand stronger assurances, and the best guarantees of employee talent come in the form of certifications.
Choosing between obtaining Certified Ethical Hacker and Offensive Security Certified Professional credentials may seem difficult to the uninitiated. Here's some vital clarification on which certs will help you outswim your professional peers.
Ethical Hacker Job Opportunities
[fa icon="calendar'] Aug 19, 2015 11:30:20 AM / by Alexandra Ducane posted in CEH, EC-Council, Ethical Hacking
Updated for 2022. As innovation in the technology field accelerates and becomes increasingly sophisticated, there are many new, exciting devices and gadgets hitting the market. While these advancements in technology have offered society a tremendous level of convenience, on the flip-side they open more opportunities for hackers. These bad actors are constantly looking for ways to exploit new systems to their benefit at the expense of innocent victims, such as card skimming and other forms of cyber crime.
With the exponential growth in advanced technology, comes increased risk of cybersecurity breaches. The demand for qualified personnel who can assess these vulnerabilities and help fix them is at an all-time high in the Washington, DC, region. So, if you're thinking about a career in ethical hacking, there is a lot to gain by obtaining the CEH certification, and understanding some of the roles you could apply for once you have it.
Here we'll break down some of the more popular job opportunities available to those with the Certified Ethical Hacking (CEH) certification!
How We Can Help You Prevent a Hacking Incident
[fa icon="calendar'] Apr 28, 2015 9:00:37 AM / by Jackie Somma posted in Online Training, Uncategorized, Ethical Hacking
The internet is full of hackers, and these hackers grow in numbers, strength, and power each and every day. It was recently discovered that a group of hackers had managed to steal in total, around $1 billion from banks through their computers. This is thought to be one of the biggest banking breaches in history, and the robbers didn't even have to physically go to the bank. These hackers got their way into the banks' computer systems and observed the banks' operations. They either set up fake bank accounts to steal money with, or they programmed ATMs to dispense money at specific times. According to Kaspersky Labs, the hackers have attacked 100 banks in 30 countries, all fairly easily. Banks are one of the more prone industries to hacking, but they're not the only ones that need to keep a watchful eye when it comes to hacking incidents.