Don't do the crime if you can't do the time.
TrainACE - IT and Cybersecurity Training Blog
Why a Career as an Ethical Hacker is Awesome
[fa icon="calendar'] Nov 10, 2014 9:00:28 AM / by Jackie Somma posted in CEH, EC-Council, Ethical Hacking
Open SSL, Being Patched Again?!
[fa icon="calendar'] Jun 9, 2014 9:15:50 AM / by Christian Crank posted in Cisco, Cybersecurity, Ethical Hacking

So OpenSSL is being patched again, very shortly after the Heartbleed Bug was fixed. According to the OpenSSL Security Advisory, multiple security vulnerabilities affecting the security layer have been recently discovered. One of the security threats actually allowed an attacker to see and modify traffic between an OpenSSL server and the client. While this news might seem bad, finding these vulnerabilities indicate that OpenSSL is frequently monitored by security professionals, and the appropriate steps are being followed to patch these vulnerabilities. This in turn makes OpenSSL a more secure implementation of the protocols SSL/TLS (Secure Socket Layer/Transport Layer Security).
Ethical Hacking Tools and Techniques
[fa icon="calendar'] Apr 4, 2014 8:00:16 AM / by Alexandra Ducane posted in CEH, EC-Council, Ethical Hacking
Top 7 Tips for Ethical Hacking
[fa icon="calendar'] Feb 11, 2014 9:43:16 AM / by Max Fonrose posted in CEH, EC-Council, Ethical Hacking
Do you possess any of these traits? Enterprising. Investigative. Inquisitive. Curious. Methodical. Calculated. Patience. Does this sound like you? Do you get excited thinking about firewalls and encrypted websites? Are you interested in being one of the good guys that help stop criminal hackers? If you fit this description, you probably are an ethical hacker or you have what it takes to become one. Do you think you have the potential to be an effective ethical hacker?
CEH Prerequisites for Training and Certification in 2021
[fa icon="calendar'] Dec 4, 2013 11:30:06 AM / by Paul Ricketts posted in CEH, EC-Council, Ethical Hacking
(** Updated March, 2023)
EC-Council's CEH Certification has become the must-have accreditation if you want to become a certified ethical hacker. While you can jump right in and take the exam with limited experience, there are some necessary CEH prerequisites and some recommended ones. Here's a breakdown of what ethical hacking is and our recommended CEH prerequisites.
CEH Practice Test
[fa icon="calendar'] Nov 20, 2013 11:30:13 AM / by alan posted in CEH, EC-Council, Ethical Hacking
The vision of a hacker sitting in a darkened room pecking away on a keyboard with computer code scrolling down three separate monitors morphs to an invaluable member of the business world. Legal hacking grabs the attention of many who want to use their computer coding and puzzling skills to earn a living instead of running from the law.
Security & Hacking Vulnerabilities in Windows 8
[fa icon="calendar'] Nov 15, 2013 10:34:55 AM / by The TrainACE Team posted in Cisco, Cybersecurity, Malware, Microsoft, Ethical Hacking
When Windows 8 debuted, it brought along a completely new interface, updated platform, and transformed user experience.
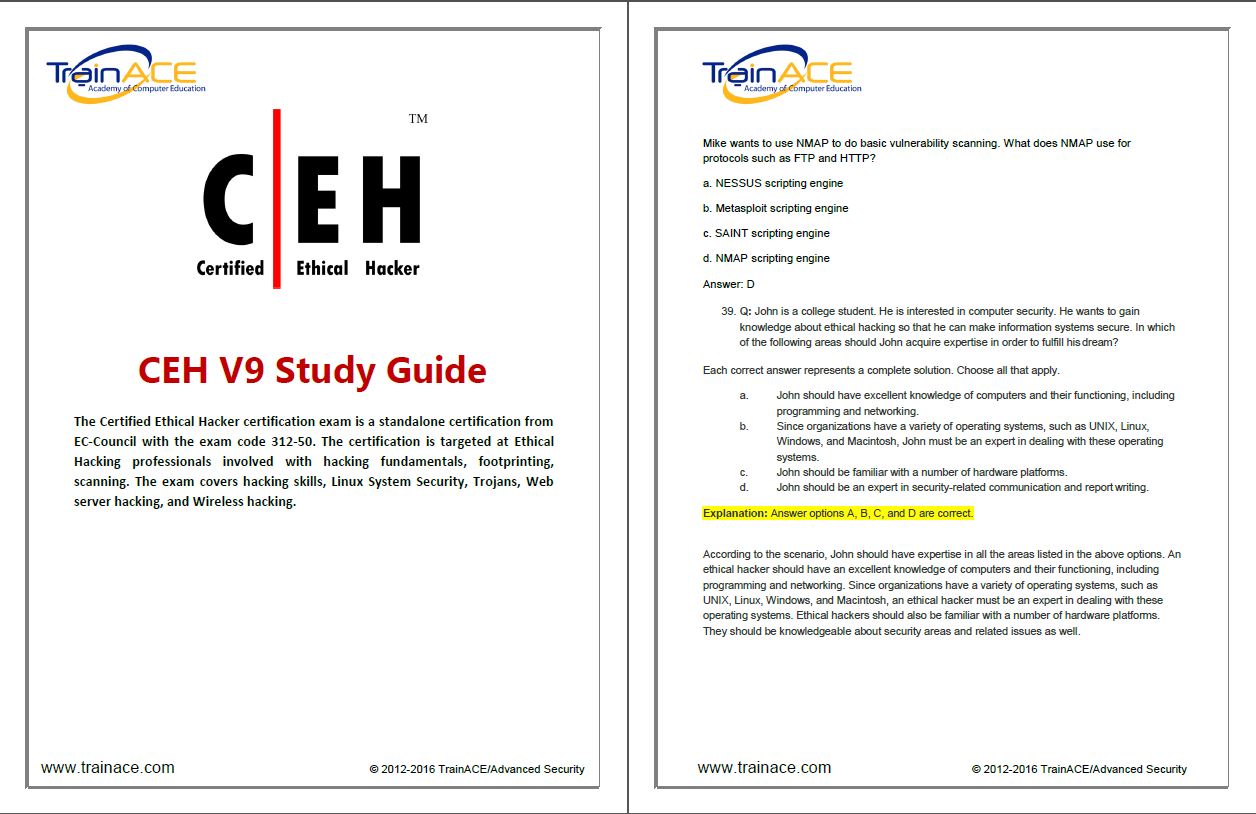
CEH Training Materials
[fa icon="calendar'] Nov 6, 2013 11:01:33 AM / by alan posted in CEH, EC-Council, Ethical Hacking
Being a certified ethical hacker is an in-demand career. While relatively new, the need for it can't be underestimated. These are the people who can beat unethical hackers, because they know the things those hackers know and can think like them. There are now classes around the world that will teach you to become a certified ethical hacker. Once you're certified, you can get a job with almost any company that uses technology that is prone to hacking. To become certified, however, you have to pass a certification exam at the end of your training course.
CEH Training Study Guide
[fa icon="calendar'] Oct 30, 2013 11:30:34 AM / by alan posted in CEH, EC-Council, Ethical Hacking
Certified Ethical Hackers (CEH) can be very beneficial for companies. By applying their training as hackers for the good of organizations, they can help test firewall systems as well as other network security features to find vulnerabilities. This knowledge can then be used to help people withstand real attacks from others with nefarious motives.
CEH Training Books
[fa icon="calendar'] Oct 23, 2013 11:30:19 AM / by alan posted in CEH, EC-Council, Ethical Hacking
In order to be prepared for Certified Ethical Hacking exams, you should invest in quality reading material. Training books on the market can provide you with everything you need to know in order to prepare for a career in CEH. After you have completed your exams, keeping your CEH books on hand for future reference is recommended. However, you'll need to keep up to date with current editions for well used books, as information in the CEH industry changes regularly. Here are some of the top texts you can use for CEH training and exam preparation.
The Importance of Secure Mobile Application Coding in Today's Fast Paced and High-Volume App Environment
[fa icon="calendar'] Oct 9, 2013 4:41:16 PM / by The TrainACE Team posted in Cisco, Cybersecurity, mobile security, wireless security, Ethical Hacking
Mobile applications have increasingly become a popular way to reach customers in today’s digitally-driven society. With over 50 million applications in the market today, the industry continues to grow at a rapid pace. By 2015, experts expect the development of mobile applications to outnumber PC projects at a ratio of four to one. But while millions of consumers are enjoying the abundance of various beneficial and useful apps, many of them are unbeknownst to the security threats several of these apps can pose—because thousands of these app developers are abandoning methods of secure coding in hopes of putting out their products as quickly as possible.
Exploring Secure Email After The Silent Circle And Lavabit Shut Downs
[fa icon="calendar'] Sep 24, 2013 5:25:28 AM / by Ryan Corey posted in Cisco, cyber war, Cybersecurity, Information Assurance, Ethical Hacking
Both Silent Circle and Lavabit recently shut down their encrypted email services. Lavabit was the first to take action following word that the United States government wanted data handed over that would violate customers' privacy. Ladar Levison, owner of Lavabit, said he faced the decision of complying with the government and betraying the American people or ending the email service he worked hard to build. He also said that he was legally unable to explain the events leading up to his decision due to recent laws passed by congress blocking his freedom of speech.