Not all hackers are cybercriminals. Increasingly, businesses around Washington DC, Maryland, and Virginia employ ethical hackers (also known as white hat hackers) to break into their computer networks to expose vulnerabilities. Ethical hacking and penetration testing have become a mainstream career within the region, with companies employing a highly skilled cohort of programmers and computer experts.
Let’s explore the basics and increase your understanding of ethical hacking. We’ll lay out the differences between Black Hat and White Hat hackers, differentiating between cybercriminals and ethical hackers.
Ethical hacking and cybersecurity are currently one of the most exciting and rewarding areas of the IT industry to work in. The field continues to grow fast, and with more job openings than skilled IT professionals to fill them, now is a time to establish yourself in a lucrative and fast-paced career. So, if the following information whets your appetite take a look at our Certified Ethical Hacker training program.

Understanding Ethical Hacking - Black Hat vs. White Hat
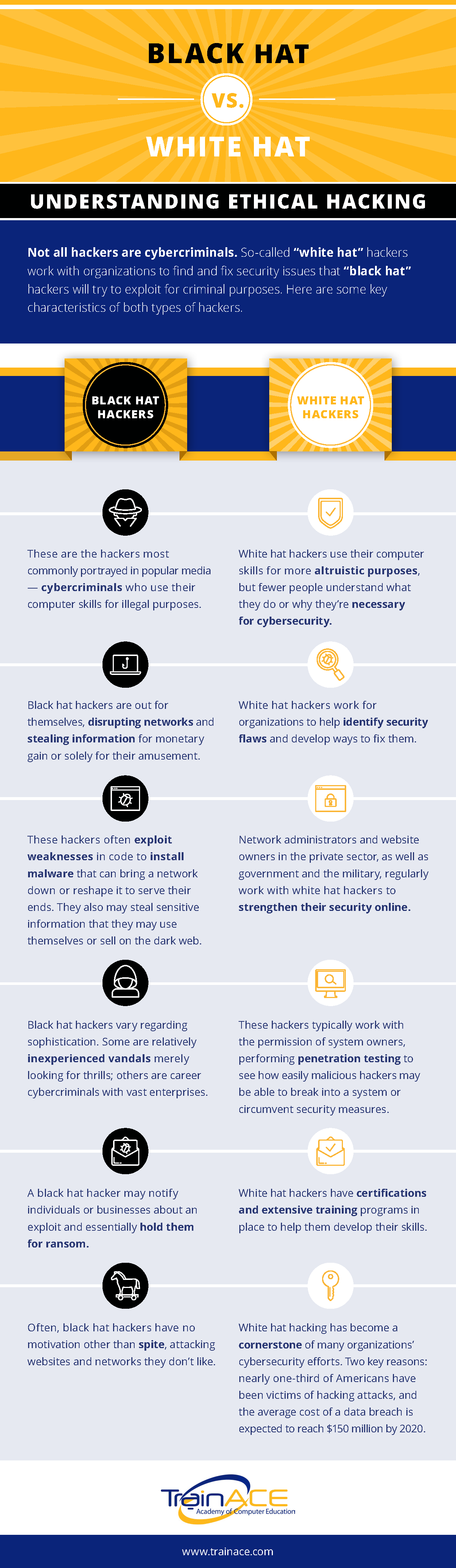
Not all hackers are cybercriminals. So-called “White-Hat” hackers work with their organizations to find and fix security issues that “Back-Hat” hackers might try to exploit for criminal purposes.
These are some key characteristics of the two types of hackers:
Black Hat Hackers
- These are the hackers who are most often portrayed in popular media. They are cybercriminals who use their computer skills for illegal purposes
- Black Hat hackers are out for themselves, disrupting networks and stealing information for monetary gain, political influence, or solely for their own amusement
- These hackers often exploit weaknesses in code to install malware that can bring a network down or shape it to serve their ends. They may also steal sensitive information that they use themselves or sell on the dark web. More often than not, these hackers exploit human behavior to initiate an attack by encouraging individuals within a target company to click on a link in an email or social media post that installs malware.
- Black Hat hackers vary regarding their sophistication. Some are relatively inexperienced vandals, merely looking for thrills; others are career criminals with vast enterprises, and then there are state-sponsored groups intent on furthering a country's political agenda.
- A black hat hacker may notify individuals or businesses about their exploit and hold them to ransom for return or unlocking files. Ransomware has become a significant issue in the US in the last few years.
- The motivation of black hat hackers varies. Some are looking to extort money, while others may be attacking websites for spite or because they hold different values than their attackers. Some are looking to exploit social discontent for political purposes.
White Hat Hackers
- White Hat hackers use their IT skills for more altruistic purposes, but fewer people outside of the IT industry have an understanding of ethical hacking, what ethical hackers do, or why they’re necessary for cybersecurity
- White Hat hackers work for organizations to help identify security flaws and develop ways to fix them
- Network Administrators and website owners in the private sector, as well as government and the military around Washington DC, regularly work with white hat hackers to strengthen their online security
- These hackers work with the permission of system owners performing penetration testing to see how easily malicious hackers may break into the system or circumvent security measures. They also use email and social media to test vulnerabilities related to human behavior, such as clicking on a bad link.
- White Hat hackers have certifications and extensive training programs in place to help them develop and prove their skills
- White Hat hacking has become a cornerstone of many organizations'’ cybersecurity efforts. Two key reasons for this are that nearly one-third of Americans have been victims of hacking attacks, and the average cost of a data breach is expected to reach $150 million by 2020
Getting into an Ethical Hacking Career
Understanding ethical hacking takes time and commitment. The fundamentals described above just scratch the surface of what you need to know to become a skilled White Hat hacker. But once you have mastered the basics and attained your first certifications (such as EC-Council’s Certified Ethical Hacker), you’ll open a wide range of job opportunities in an exciting and constantly developing field of the IT industry.
If you’re starting with little or no experience, you’ll want to investigate taking CompTIA A+ and CompTIA Network+ training and certification. This will get you started and prepare you for certifications like Security+ or CEH, which are the starting points for cybersecurity careers. If you have some solid IT experience, you may be able to jump straight into Security+ or CEH certification training. Check out our information on CEH.
Leave Your Comment Here